Sécurité Zero Trust avec Zscaler et AWS
Une transformation numérique sécurisée requiert une nouvelle approche
Les outils traditionnels élargissent les surfaces d’attaque et facilitent les déplacements latéraux.
Le backhauling du trafic pour garantir la sécurité provoque des congestions et ralentit les performances.
La sécurité et les réseaux existants rendent ce processus complexe, long et coûteux.
Les données se déplacent hors site et s’éloignent des outils de sécurité du périmètre.
Les outils traditionnels ne peuvent pas sécuriser les communications des charges de travail dans le cloud.
Les erreurs de configurations sur AWS augmentent le risque de violation de données et de non-conformité.


Ruba Borno | Vice-président des chaînes et alliances mondiales chez AWS.
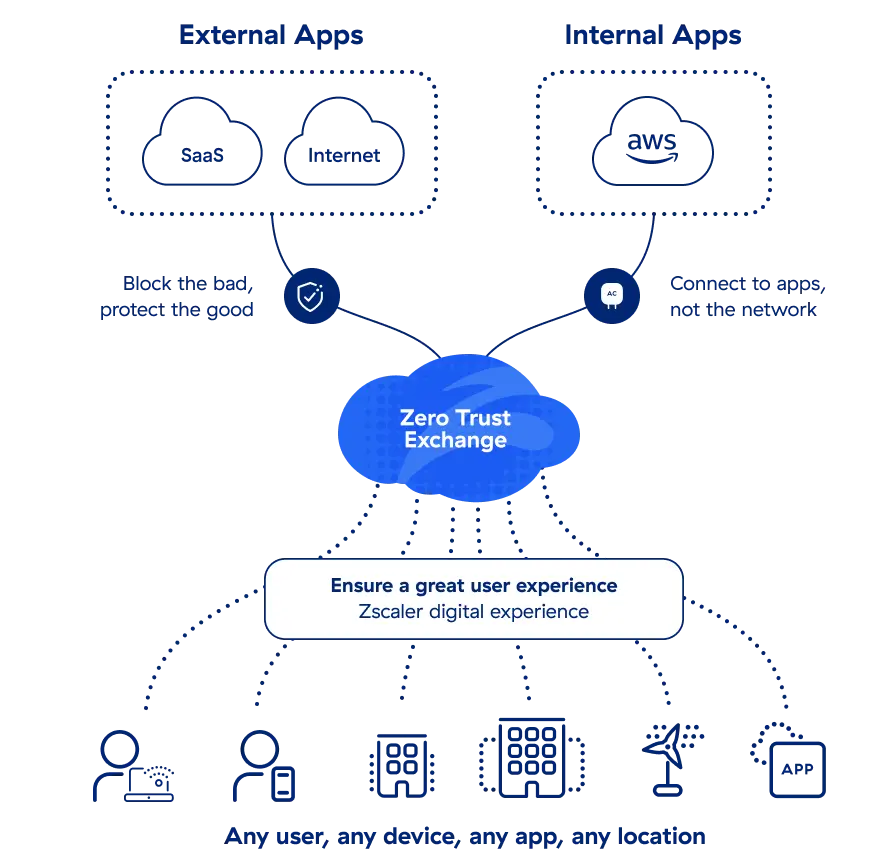
Plateforme Zscaler Zero Trust Exchange
Zscaler Zero Trust Exchange™ connecte en toute sécurité les utilisateurs aux applications et aux charges de travail dans AWS sans accéder au réseau d’entreprise. Contrairement aux solutions de sécurité basées sur le périmètre, la sécurisation d’AWS avec Zscaler permet de :
- Minimiser la surface d’attaque
- Empêcher le déplacement latéral des menaces
- Empêcher toute compromission et perte de données
- Améliorer les expériences digitales
- Réduire les coûts et la complexité


« Nous sommes très satisfaits de Zscaler et d’AWS. Ils nous ont permis de nous déployer en toute sécurité dans le cloud à grande échelle… »
Eric Fisher
Directeur informatique des systèmes d’entreprise
GROWMARK, Inc.

« Nos développeurs adorent ZPA. Ils peuvent accéder rapidement, facilement et en toute sécurité aux applications et charges de travail privées dans AWS. »
Michael Jacobs
RSSI adjoint
Mindbody

« Avec Zscaler, nos développeurs peuvent aller directement au but dans notre empreinte AWS et commencer à travailler. »
Jeff Negrete
Vice-président, Infrastructure et opérations
Verisk
Comment Zscaler et AWS assurent le Zero Trust
Zscaler fournit l’architecture Zero Trust et les solutions spécialisées qu’il vous faut pour sécuriser vos déploiements AWS.
Fournissez un accès Zero Trust aux applications internes sur AWS pour tout utilisateur, n’importe où.
Sécurisez les communications et les configurations de vos charges de travail AWS.
Protégez les données sensibles dans, et en mouvement vers, les offres AWS telles que S3.
Les plus grandes entreprises mondiales nous font confiance

















Zscaler sur AWS GovCloud
Zscaler et AWS fournissent des solutions Zero Trust pour les agences gouvernementales. Nous avons tout ce dont vous avez besoin pour sécuriser vos utilisateurs, vos données et vos charges de travail