Blog Zscaler
Recevez les dernières mises à jour du blog de Zscaler dans votre boîte de réception
S'abonnerCoverage Advisory for 3CX Supply Chain Attack
Update [2023-03-31 05:00 PM PST] We have published a blog detailing our analysis on the 3CX Supply Chain Attack.
Background
On 30th March 2023, 3CX released a security alert for 3CX Electron Windows App shipped in Update 7, which informed users about a supply chain attack. The issue has affected the executables for both Windows and Mac operating systems.
What is the issue?
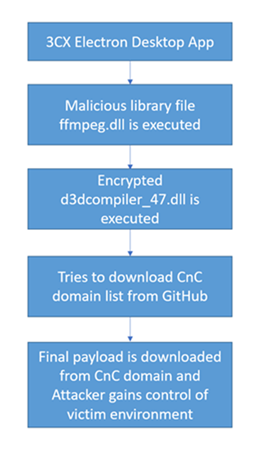
The impacted 3CX Electron Desktop App was bundled with an infected library file named ffmpeg.dll. This infected library further downloads another encrypted file d3dcompiler_47.dll. This file has functionality to access .ico files hosted on GitHub which contain CnC information. These CnC domains are used to deliver the final payload which allows the attacker to perform malicious activity in the victim’s environment. The diagram below shows the attack chain.
During our investigations we found the attacks to be active since February, we will release a more detailed analysis report soon.
What systems are impacted?
This impacts Windows and Mac versions of 3CX Electron Windows App.
- 3CX Electron Windows App version 18.12.407
- 3CX Electron Windows App version 18.12.416
- 3CX Electron Mac App version 18.11.1213
- 3CX Electron Mac App version 18.12.402
- 3CX Electron Mac App version 18.12.407
- 3CX Electron Mac App version 18.12.416
What can you do to protect yourself?
- If you find systems on your network running these compromised versions of 3CX Electron Desktop app then please uninstall the software.
- Find the infected systems by checking the client details from your SIEM logs for systems trying to connect to the IoCs mentioned in the IoC section of this advisory.
- While the reputation based blocks will block communication to the CnC domains, the CnC communication uses HTTPS protocol, please enable SSL inspection for the content downloaded from such malicious domains to be scanned.
Zscaler Coverage
Advanced Cloud Sandbox
- Win32.Trojan.3CX
Advanced Threat Protection
- Win32.Trojan.3CX
- HTML.MalURL.Gen.XO
IoCs
CnC domains:
- raw[.]githubusercontent[.]com/IconStorages/images/main/
- visualstudiofactory[.]com
- sourceslabs[.]com
- sbmsa[.]wiki
- qwepoi123098[.]com
- journalide[.]org
- dunamistrd[.]com
- azureonlinestorage[.]com
- azureonlinecloud[.]com
- akamaicontainer[.]com
- zacharryblogs[.]com
- Soyoungjun[.]com
- pbxsources[.]com
- pbxphonenetwork[.]com
- pbxcloudeservices[.]com
- officestoragebox[.]com
- officeaddons[.]com
- msstorageboxes[.]com
- msstorageazure[.]com
- msedgepackageinfo[.]com
- glcloudservice[.]com
- azuredeploystore[.]com
- akamaitechcloudservices[.]com
Malicious hash
- d5101c3b86d973a848ab7ed79cd11e5a
- ca5a66380563ca4c545f1676c23bd95d
- 6426fe4dc604c7f1784ed1d48ab4ffc8
- 82187ad3f0c6c225e2fba0c867280cc9
- 74bc2d0b6680faa1a5a76b27e5479cbc
- f3d4144860ca10ba60f7ef4d176cc736
- bb915073385dd16a846dfa318afa3c19
- 9833a4779b69b38e3e51f04e395674c6
- 0eeb1c0133eb4d571178b2d9d14ce3e9
Details related to the threat signatures released by Zscaler can be found in the Zscaler Threat Library.
Cet article a-t-il été utile ?

Recevez les dernières mises à jour du blog de Zscaler dans votre boîte de réception
En envoyant le formulaire, vous acceptez notre politique de confidentialité.




