Read more posts like this on Zscaler's CXO REvolutionaries.
Our increasingly entrenched and extensive use of technology in nearly every facet of life urgently calls for security solutions that keep our networks and data safe. While some companies are keeping pace, many are working to upgrade their infrastructures and can miss key gaps in cybersecurity. The latest spate of ransomware attacks across large enterprises with deep pockets and public agencies suggests no one is immune.
And this is not the time to make an error. In 2020 alone, data breaches due to ransomware attacks had an average price tag of $4.4 million. This number does not include the impact of ransomware, destructive malware, or hijacked logins and identities. Firms scrambling to ward off attacks from tech-savvy and tactical hackers are driving a booming investment in cybersecurity consulting and solutions. The market is expected to reach $418 billion by 2028. The increase in cybersecurity spending is a reaction to the increase in cyberattacks. In the last year, 43% of businesses were targeted. And data isn’t the only thing on the line.
How has the cyberthreat against your organization in your view developed?
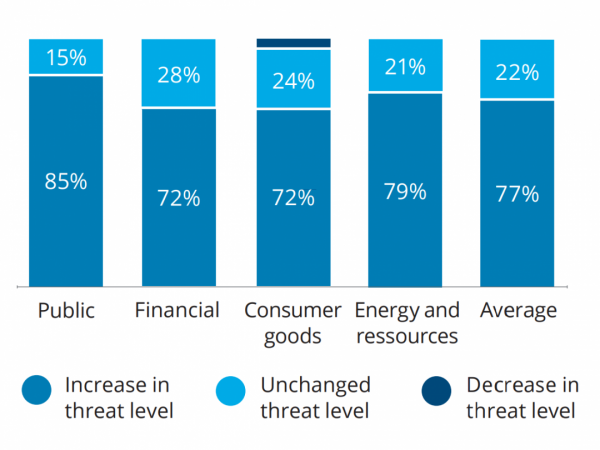 2020 Deloitte Cyber Survey: Cyber Security Leadership Chart
2020 Deloitte Cyber Survey: Cyber Security Leadership Chart
What is truly at risk with cybersecurity?
The threat of data corruption and privacy infractions grows with each passing day. The increased reliance on remote and hybrid work only expedited the damage from security flaws previously exploited on cloud systems and open networks. Companies implementing 5G networks or leveraging the Internet of Things (IoT) approach stand to lose much if they succumb to a cyberattack.
But by no means should corporations halt progress due to security fears. And they aren’t: Nearly 80% of companies are rolling out new tech innovation without the means to secure it, and a system breach brings a breach of trust with customers and stakeholders. The result is almost always the same: business operations are disrupted, data is lost or stolen, and the bottom line suffers.
Who is truly responsible for cybersecurity infractions?
Gone are the days of pushing off technical problems to IT teams. Technology is the core of most modern business enterprises, and that reliance is only becoming more pronounced as time goes on.
While we need knowledgeable IT teams in place to implement, monitor, and maintain these systems, the responsibility for their purchase and efficacy falls largely on management. This does not preclude publicly traded companies with a board of director oversight.
In fact, as was the case with Target and Equifax, leadership has had to take responsibility for data breaches and their repercussions. The Target legal settlement required an implementation of a security program, independent security assessment, AND executive responsibility moving forward.
While the Business Judgment Rule provides comprehensive protections, the courts have considered personal liability for improper security measures and the failure of board members or directors to take reasonable action and responsibility for the prevention of what are often considered preventable situations.
And the penalties can be steep and damaging. On top of data loss and a detrimental economic toll on the company, litigation and change management can be costly and time consuming. Cybersecurity regulators, such as the Office of the Comptroller on Currency, are also imposing fines on a massive financial scale for infractions.
How to address cybersecurity governance
With risk management cascading from directors down to implementation teams, staying informed and being proactive is critical. But how can a board of directors, which is most likely not composed of cybersecurity experts, approach cybercrime risk mitigation from a leadership perspective? In one survey of enterprises, only slightly more than a third of respondents reported reviewing security concerns at least monthly.
How often is cybersecurity on the top leadership’s agenda?
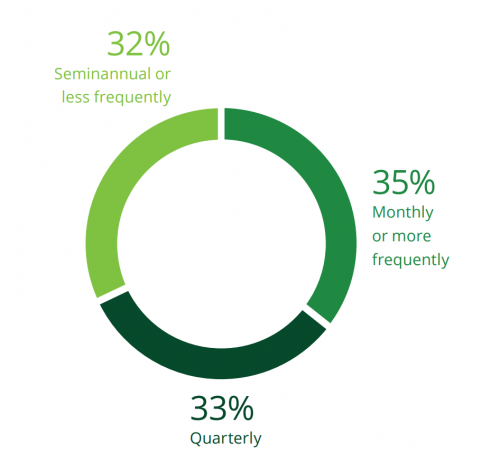 2020 Deloitte Cyber Survey: Cyber Security Leadership Chart
2020 Deloitte Cyber Survey: Cyber Security Leadership Chart
Proactive demonstration of due diligence is a great starting point. Tapping into experts and (somewhat ironically) technology solutions to fill knowledge gaps is another. PwC recommends that boards explore the benefits of NIST CSF to foster effective communication and processes among all stakeholders.
Here, we’ll explore a few ways directors can seek and achieve better cybersecurity governance for their organizations. The key is to approach this largely like other content areas where directors may not be specific thought leaders. Education, information, and dissemination can counter previously inadequate, hands-off, and even lackluster efforts.
Realize the bigger picture
You can’t know what you don’t know. A board of directors should start by reviewing reports from IT leaders and stakeholders in the organization. Bring in the experts and ask for a complete assessment of known gaps as well as evolving changes in your tech stack.
You may need to design or implement additional reporting to ensure that your understanding is formed on a data- and fact-based level. From there, you can use the information to gain better knowledge of challenges, achievements, and recommended actions for improved cybersecurity policies moving forward.
Assign security oversight responsibility
Someone on the board (either a single member or a committee) should be assigned responsibility for learning the ins and outs of the company’s security needs and status. These individuals can provide ongoing updates and present larger issues for the broader board to assess and vote on.
Committee members don’t have to be experts, but they can evolve into specialists. They can rely on internal specialists, third-party consultants, vendors, and technology solutions to plan ahead and better understand the landscape.
Leverage objective measures
Risk assessment is an ongoing process with new vulnerabilities surfacing daily. Bringing in third parties to identify loopholes in security compliance through methods like ethical hacking can be quite insightful. Security consultants and supporting software applications can give great insight into the potential risks for your network.
Consider a zero trust mentality
As the name implies, the zero trust model assumes that anything attempting to enter, leave, or relocate within a network cannot be trusted and should be verified or cleared by a governing system. This can give companies a significant advantage given the patchwork of on-premise and cloud solutions, proprietary and third-party applications, and closed networks and shared access.
Add remote work and innumerable devices to the mix, and the idea of trusting nothing can suddenly seem like the safest route. Companies can plug existing holes in their infrastructure and reduce long-term risk with this approach, and boards stand to learn much by researching this option.
Create a culture of transparency
While you certainly do not want to share details about any outstanding gaps in your cybersecurity protocols, transparency can still present benefits. In the event of a breach, disclose anything that should be declared to stakeholders and customers. This instills faith and trust that the board is doing everything in its power to address issues, protect data, and take ownership of any failings.
The path forward is constantly shifting
Above all, a board of directors must understand that cybersecurity is a dynamic discipline that requires unending monitoring and innovation. Laying the groundwork for reduced risk is essential but so is the knowledge that risk will always be there.
Companies should also assess their existing insurance policies, whether they adequately cover asset value in the event of a breach, and if dedicated cyber insurance may help further mitigate risk. But no matter the size of your insurance policy, leadership must remain involved and educated in cybersecurity for the business and prepare policies and procedures in the event of a breach with an eye toward responsibility.






